Many marketers invest in proxies expecting instant invisibility, only to face blocks within minutes. The truth is, not all proxies work equally against modern anti-bot systems. Understanding how proxies actually evade detection mechanisms, from IP masking to request distribution, determines whether your automation succeeds or fails. This guide breaks down proxy types, success rates against leading bot managers, and practical strategies to choose solutions that keep your operations undetected in 2026.
Table of Contents
- How Proxies Mask IP Addresses And Evade Detection
- Understanding Proxy Types And Their Security Features
- Effectiveness Of Different Proxies Against Modern Anti-Bot Detection
- Practical Guidance For Choosing And Using Proxies To Bypass Anti-Bot Systems
- How Proxy Poland Helps You Bypass Anti-Bot Detection In 2026
Key takeaways
| Point | Details |
|---|---|
| IP masking prevents blocks | Proxies hide your real IP address, letting you bypass reputation-based bans and geo-restrictions effectively. |
| Proxy type drives success | Residential and mobile proxies outperform datacenter options on protected targets due to authentic IP origins. |
| Cost efficiency matters | Calculate cost per successful request, not just bandwidth, since failed attempts waste resources on protected sites. |
| ASN classification happens early | Detection systems identify proxy IPs by network origin before reading headers, making IP source critical. |
| Strategic rotation mimics users | Distributing requests across multiple IPs and managing rates helps your traffic appear organic to anti-bot systems. |
How proxies mask IP addresses and evade detection
Proxies function as intermediaries between your device and target servers, replacing your real IP address with one from the proxy network. This fundamental capability lets you avoid IP-based blocks, access geo-restricted content, distribute requests, and manage rate limits across multiple connections. When you route traffic through a proxy, the target server sees only the proxy IP, preventing your actual location and identity from being logged or blocked.
Anti-bot systems rely heavily on IP reputation databases that track suspicious activity patterns. If your IP has a history of automated requests or belongs to a known proxy network, detection happens instantly. Quality proxies solve this by providing clean IPs with no negative history, often from residential ISP pools or mobile carriers that look identical to regular users. This masking prevents immediate classification as a bot.
Geo-restrictions pose another challenge that proxies elegantly bypass. Many platforms serve different content or block access entirely based on geographic location. By connecting through a proxy located in the target region, you appear as a local user, gaining full access to region-locked content. This technique proves essential for market research, ad verification, and competitive analysis across different territories.
Request distribution across multiple proxy IPs creates organic traffic patterns that evade rate limiting. Instead of sending 1,000 requests from one IP (an obvious bot signal), spreading those same requests across 50 IPs makes each connection appear like a normal user browsing casually. This distributed approach prevents triggering volume-based detection thresholds that flag unusual activity spikes.
Pro Tip: Test your proxy setup regularly using a proxy speed test to verify both anonymity and performance before deploying at scale.
Managing request rates complements IP distribution by controlling how quickly you access target sites. Even with multiple IPs, sending requests too rapidly from each one signals automation. Smart rate limiting mimics human browsing speeds, adding random delays between requests to match natural user behavior patterns. This temporal distribution works alongside IP rotation to create convincing organic traffic.
Early detection systems classify IPs based on ASN (Autonomous System Number) and network origin within milliseconds of connection, often before any HTTP headers are transmitted.
Understanding these core masking functions helps you evaluate which proxy types deliver the security and anonymity your specific use case demands.
Understanding proxy types and their security features
HTTP proxies represent the most basic option, routing only web traffic without encryption. These cost-effective proxies handle basic web navigation but offer limited security since data travels in plain text. They work fine for simple tasks like accessing public web pages but fail when targets require encrypted connections or when you need to protect sensitive data from interception.
HTTPS proxies add encryption through SSL/TLS protocols, securing data transmission between your device and the proxy server. This encryption prevents third parties from reading your traffic, making HTTPS proxies suitable for handling login credentials, payment information, or any sensitive automation tasks. The added security comes with minimal performance overhead, making them a smart default choice for most web scraping projects.
SOCKS5 proxies operate at a lower network level, handling diverse traffic types beyond just HTTP while offering robust security. They support any protocol or application, from email clients to gaming traffic, providing maximum flexibility. The tradeoff is complexity, SOCKS5 requires more technical configuration than HTTP proxies but rewards you with better performance and protocol versatility. Learn more about choosing the right protocol in our proxy protocols guide.
| Proxy Type | Encryption | Protocol Support | Detection Risk | Best Use Case |
|---|---|---|---|---|
| HTTP | None | HTTP only | High | Basic web browsing |
| HTTPS | SSL/TLS | HTTP/HTTPS | Medium | Secure web scraping |
| SOCKS5 | Optional | All protocols | Medium | Multi-protocol automation |
| Datacenter | Varies | All protocols | High | High-volume unprotected targets |
| Residential | Varies | All protocols | Low | Protected sites, social media |
| Mobile | Varies | All protocols | Very Low | Advanced bot detection bypass |
Datacenter proxies come from cloud hosting providers like AWS, Google Cloud, or dedicated proxy companies. These IPs originate from data centers rather than residential ISPs, making them faster and cheaper but easier to detect. Anti-bot systems maintain databases of datacenter IP ranges, allowing instant identification and blocking. They still work well on unprotected targets where speed and cost matter more than stealth.

Residential proxies use real IP addresses assigned by internet service providers to actual homes and businesses. This legitimate origin makes them significantly harder to detect and block since they appear identical to regular users. The IPs come from real devices on residential networks, providing authentic digital footprints that pass most verification checks. Higher costs reflect the scarcity and value of these genuine residential connections.
Mobile proxies leverage IP addresses from cellular carriers, routing traffic through real mobile devices connected to 4G or 5G networks. These represent the hardest proxy type to detect because mobile IPs constantly rotate naturally as users move between cell towers, and carriers assign IPs dynamically. Platforms rarely block mobile IPs aggressively since doing so would affect millions of legitimate mobile users, giving mobile proxies exceptional success rates against even the most sophisticated anti-bot systems.
Effectiveness of different proxies against modern anti-bot detection
Real-world performance varies dramatically across proxy types when facing advanced bot management systems. Datacenter proxies achieve 60-90% success rates on unprotected targets but drop to 20-40% when sites deploy Cloudflare Bot Management, Akamai Bot Manager, or similar enterprise solutions. This massive decline happens because these systems instantly recognize datacenter ASNs and apply stricter verification, often blocking requests outright or serving CAPTCHAs.
Residential proxies deliver 85-99% success rates on the same protected targets, demonstrating their superior ability to bypass sophisticated detection. The legitimate ISP origin of residential IPs passes initial ASN checks, allowing requests to proceed with minimal friction. This performance gap becomes critical when scraping at scale, where even small percentage differences multiply into thousands of failed requests and wasted resources.
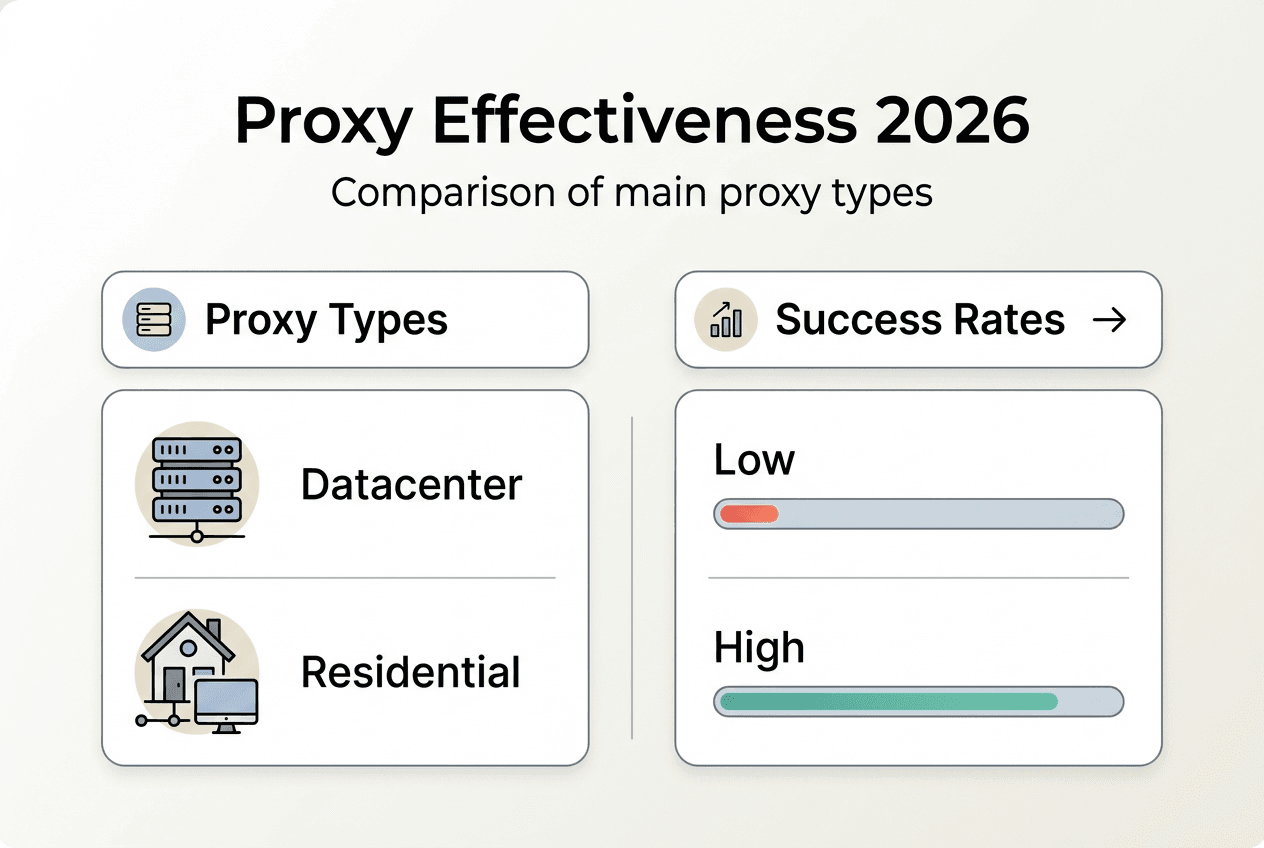
Mobile proxies frequently outperform both datacenter and residential options, especially on platforms that see heavy mobile traffic like Instagram, TikTok, or e-commerce apps. Social media sites expect most users to access via mobile devices, making mobile IPs the least suspicious option. The dynamic IP rotation inherent to mobile networks adds another layer of authenticity, since carrier IPs naturally change as devices move between towers. Discover more about mobile proxy advantages in our mobile proxies benefits guide.
Pro Tip: When evaluating proxy providers, request test credentials and run small-scale trials against your specific target sites before committing to large purchases.
ASN classification explains why detection often happens before any HTTP traffic is analyzed. Detection systems classify your IP's network origin within the first milliseconds of TCP connection establishment, examining the autonomous system number associated with the IP. Datacenter ASNs trigger immediate suspicion flags, while residential and mobile carrier ASNs receive trust scores that allow normal processing. This early classification means even perfect browser fingerprints and headers cannot save a datacenter proxy from detection on well-protected targets.
| Target Protection Level | Datacenter Success | Residential Success | Mobile Success | Cost Efficiency Winner |
|---|---|---|---|---|
| No protection | 85% | 98% | 99% | Datacenter |
| Basic (rate limiting) | 70% | 95% | 98% | Datacenter |
| Moderate (Cloudflare free) | 40% | 90% | 95% | Residential |
| Advanced (enterprise bot mgmt) | 25% | 88% | 94% | Residential/Mobile |
| Maximum (financial/ticketing) | 10% | 75% | 90% | Mobile |
Cost efficiency calculations must account for success rates, not just bandwidth pricing. Cost-per-successful-request often makes residential proxies cheaper in total on protected targets, despite higher per-GB costs. When datacenter proxies fail 70% of requests, you burn bandwidth on failed attempts while still needing to retry until success. Residential proxies succeeding 90% of the time waste far less bandwidth overall, reducing total project costs even at premium pricing.
On protected targets, the cost math flips entirely when calculating cost per successful request instead of cost per gigabyte, since you burn far less bandwidth on failed attempts with higher-quality proxies.
This analysis reveals why matching proxy type to target protection level determines both technical success and budget efficiency.
Practical guidance for choosing and using proxies to bypass anti-bot systems
Start by assessing your target's detection sophistication to match the appropriate proxy type. Social media platforms, financial sites, and ticketing systems deploy enterprise-grade bot management requiring mobile or residential proxies. E-commerce sites without Cloudflare or similar protection often work fine with quality datacenter proxies. Testing small batches against your specific targets reveals which proxy tier delivers acceptable success rates before scaling operations.
- Identify your target's protection level by attempting access from known datacenter IPs and observing block rates or CAPTCHA frequency.
- Match proxy type to detection sophistication, using mobile for maximum protection, residential for moderate defenses, datacenter only for light or no protection.
- Implement IP rotation strategies that distribute requests across multiple IPs with realistic timing intervals between uses of each IP.
- Configure protocol selection based on security needs, choosing HTTPS or SOCKS5 for encrypted traffic, HTTP only for basic public data.
- Monitor success rates continuously and adjust proxy sources when block rates increase, since IP pool quality changes over time.
IP rotation mimics organic user behavior by preventing any single IP from generating suspicious request volumes. Set rotation intervals based on target sensitivity, some sites flag IPs making more than 10 requests per minute while others tolerate hundreds. Random rotation adds unpredictability that further disguises automation, making traffic patterns harder to fingerprint. Compare mobile and residential rotation strategies in our mobile vs residential proxy guide.
Protocol selection impacts both security and compatibility with your automation stack. HTTPS proxies work with most web scraping tools and provide essential encryption for sensitive data. SOCKS5 offers maximum flexibility when you need to proxy non-HTTP traffic or want lower-level control over connections. Proxies serve as essential tools specifically because they overcome challenges posed by anti-bot systems through these technical capabilities.
Pro Tip: Use the proxy rotation calculator to determine optimal IP pool sizes and rotation schedules based on your request volume and target rate limits.
Integration with automation tools requires careful configuration to avoid leaking your real IP through DNS requests, WebRTC, or other side channels. Most scraping frameworks like Scrapy, Puppeteer, or Selenium support proxy configuration, but you must explicitly route all traffic including DNS lookups through the proxy. Test for leaks using online checkers that reveal whether your real IP appears anywhere in the connection.
Regular testing maintains proxy effectiveness as providers rotate IP pools and targets update detection systems. Run daily checks measuring success rates, response times, and anonymity levels across your proxy inventory. Replace underperforming IPs promptly since quality degrades over time as IPs accumulate negative reputation from other users. Automated monitoring alerts you to sudden drops in success rates that signal detection system updates requiring strategy adjustments.
Avoiding common pitfalls saves money and prevents detection. Never reuse the same IP too quickly, allow cooling periods between sessions from each IP. Randomize user agents, headers, and timing to prevent fingerprinting beyond just IP rotation. Respect rate limits even when technically capable of faster scraping, since aggressive behavior triggers detection regardless of proxy quality. These operational practices combine with quality proxies to achieve reliable undetected access.
How Proxy Poland helps you bypass anti-bot detection in 2026
When you need mobile proxies that consistently bypass sophisticated anti-bot systems, 4G mobile proxies from Poland deliver authentic carrier IPs from physical SIM cards and modems. Each proxy provides a dedicated connection with zero sharing, eliminating the risk of IP contamination from other users' activities. The infrastructure supports instant 2-second IP rotation, letting you adapt quickly when targets update their detection rules.
Web scraping projects benefit from proxies optimized specifically for web scraping challenges, with protocol support for HTTP, SOCKS5, OpenVPN, and Xray. The 30-100 Mbps dedicated bandwidth ensures your automation runs at full speed without throttling or connection drops. Setup completes in 10 seconds, getting your operations running immediately without complex configuration.
Plan your IP rotation strategy effectively using the proxy rotation calculator tool to determine optimal pool sizes and request distribution. This planning prevents over-rotation that wastes IPs or under-rotation that triggers rate limits. The combination of genuine mobile IPs, flexible protocols, and strategic rotation delivers the undetected access your automation demands in 2026.
FAQ
What types of proxies work best to bypass anti-bot detection?
Residential and mobile proxies consistently deliver the highest success rates against advanced anti-bot systems because their IP addresses originate from legitimate ISPs and mobile carriers. These authentic sources pass ASN classification checks that immediately flag datacenter proxies. Mobile proxies often perform best on social media and mobile-first platforms where cellular traffic is expected and trusted.
How does ASN classification impact proxy detection?
Detection systems classify your IP's network origin during initial connection establishment, examining the autonomous system number before any HTTP data is transmitted. Datacenter ASNs trigger suspicion flags that lead to blocks or CAPTCHA challenges, while residential and mobile carrier ASNs receive trust scores allowing normal access. This early classification makes IP source more critical than browser fingerprints or headers for bypassing detection.
Why is cost-per-successful-request more important than cost-per-GB?
Cost-per-successful-request provides a more accurate metric than bandwidth pricing when evaluating proxy efficiency on protected targets. Cheap datacenter proxies that fail 70% of requests waste bandwidth on failed attempts while forcing expensive retries. Premium residential proxies succeeding 90% of the time consume less total bandwidth and require fewer retries, often resulting in lower overall project costs despite higher per-GB rates. Calculate true costs using our proxy cost calculator.
How often should I rotate proxy IPs to avoid detection?
Rotation frequency depends on target sensitivity and your request volume, but most protected sites benefit from rotating after 5-20 requests per IP. Social media platforms require aggressive rotation, sometimes after each request, while e-commerce sites tolerate longer sessions. Implement random rotation intervals rather than fixed patterns to prevent detection systems from identifying your automation rhythm. Monitor block rates to find the optimal balance between rotation overhead and detection avoidance.
Can proxy headers or fingerprints bypass detection without quality IPs?
No amount of header manipulation or browser fingerprint spoofing compensates for a detected proxy IP address. Anti-bot systems perform ASN classification before reading any HTTP headers, blocking suspicious IPs immediately. Quality residential or mobile IPs provide the foundation, while proper headers and fingerprints add additional layers of authenticity. Focus first on IP quality, then optimize headers and automation behavior to match organic user patterns.